Safeguard Against Ransomware
With the alarming rise in ransomware attacks targeting businesses and individuals worldwide, it has become imperative to adopt proactive measures to mitigate the damaging consequences of these cyber threats. While prevention strategies play a significant role in mitigating risks, backup solutions...

Why Outsource Data Protection?
Data protection is an essential aspect of running a business. With the increasing complexity of technology and the ever-growing amount of data, it's becoming more challenging for companies or IT teams to manage it independently.

Reasons to backup O365
The reality is that while Microsoft provides infrastructure resilience, data protection remains your responsibility. And without third-party backup, sensitive business data such as emails or shared files stored in Microsoft 365 are not protected from the most common or most serious data loss...

Cloud Backup Pricing Calculator

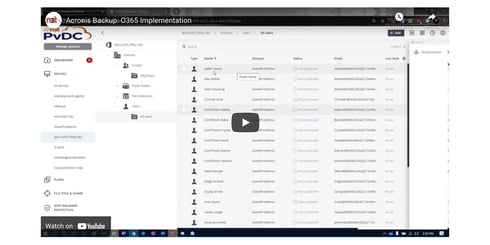
365 Backup
How to ensure your Microsoft 365 data is backed up.
Chances are, right now you have a Microsoft 3654 application open. Over 1 million companies around the world rely on the suite of Outlook, OneDrive, OneDrive, Word, Excel, PowerPoint, OneNote, and Microsoft Teams on a daily basis. They're...

Cloud Backup Checklist
There can be quite a few challenges when it comes to backing up your sensitive data. This comprehensive checklist goes step by step on how to make a backup plan and the following action items that follow. From discovering what needs to be protected, to the audit and testing process, use this...
Common Backup Challenges: Whitepaper
Data is the lifeblood of a business and it's up to IT Departments to keep it accessible and protected. With the ever changing landscape of networks, storage growth, the current (and intense) focus on security, and more professionals working from home, there are many challenges that IT professionals...
Cloud Migration Checklist
At this point, you know moving your data to the cloud is a good move for the business. Financially it makes sense, efficiency has been proven, and security has been evaluated - it's time to make the move. However, it is important to be aware of the challenges you may face during a migration project...

2022 Cloud Security Trends: eBook
Throughout the past decade, many companies made the switch from hosting data on premises to the cloud, now that those companies have migrated - how can they keep their data secure and continue to improve their data protection strategy?
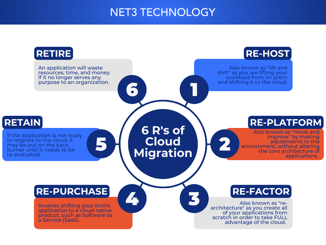
6 R's of Cloud Migration
Migrating to the cloud can be challenging when determining the best migration strategy for your applications and systems. For a further explanation of the 6 R's of Cloud Migration: Re-host, Re-platform, Re-factor, Re-purchase, Retain, and Retire, download this Whitepaper to fully understand what...