
Maintaining a solid security stance in 2022 is a daunting task, especially for smaller IT teams. The world of cybersecurity is evolving at a breakneck pace, and defining what is needed to protect your organization is getting more difficult all the time. It is very easy for an IT organization to get outpaced by current trends in malicious activity.
We are going to break down some of the trends we see in our work, and how we can address them to keep our organizations data, reputation, and business safe.
Increased Adversarial Intelligence
Ransomware and exploitation of networks are becoming much less random and more of a targeted event. Threat actors are beginning to move away from spray and pray phishing emails. Although the vast majority (54%) of ransomware attacks come from phishing, we are increasingly seeing a phenomenon known as whale hunting.
When whale hunting, extensive reconnaissance is done by the threat actors to determine a target with enough cash and a big enough vulnerability to make it worth their while. Once they have a target, they are using extremely sophisticated methods to obtain more information. In some cases we have seen law enforcement emails being spoofed to send "Emergency Data Requests" to ISP's and Cloud Providers for details of the customer networks and accounts. Using that information, they can make more informed choices about which vulnerabilities to attack first.
In March of 2021, Broward County School District in Florida was breached and 1.5 TB of data was exfiltrated by the threat actors. Enough reconnaissance was done that the threat actors knew their ransom demand (which was 40 million dollars) only made up 1% of the school systems budget. They mentioned this during negotiation and repeatedly made the point that they had access to and had examined the budgets for the school district, see below.
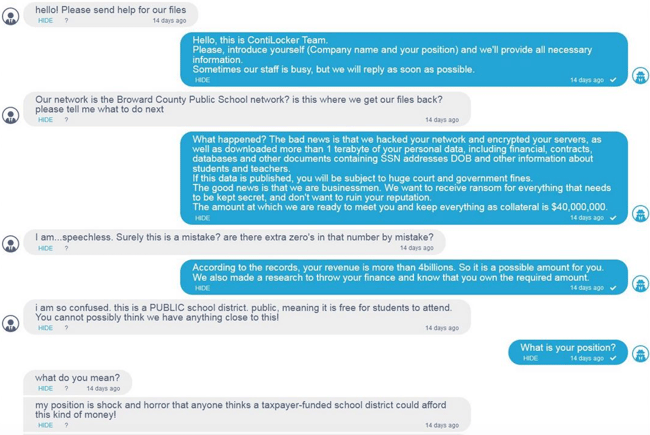
This shows the advanced knowledge of the target, going well beyond the technical considerations. The school system refused to pay the ransom, and all the data including personal details of 50,000 employees and school children were leaked online. Although BCPS did the right thing in not paying the ransom and were able to recover their network and file systems, the additional threat of leaked data was not addressed. DLP (Data Loss Prevention) technology and early detection of the breach would have prevented much of this issue.
Attacking the Weakest Link
Although the intelligence gathering and hard reconnaissance techniques are evolving and coming to the forefront, threat actors are sharpening their skillset on the soft side as well. People in an organization are the greatest threat to the organization. This is a hard learned lesson that creates a lot of friction between IT departments and the user base that they serve.
The Lapsus$ ransomware gang became a prime example of how social engineering techniques can cause big damage to the organization. Lapsus$ would work from the employee up, gaining access to authorized credentials through bribery, impersonation, and SIM swapping techniques. Once they had gained credentials, they would use the internal company toolsets to wreak havoc and gain actionable intel on the targeted company.
"Their tactics include phone-based social engineering; SIM-swapping to facilitate account takeover; accessing personal email accounts of employees at target organizations; paying employees, supplies, or business partners of target organizations for access to credentials and multi-factor authentication (MFA) approval; and intruding in the ongoing crisis communication calls of their targets." - Microsoft Commented
People are a difficult factor in the cybersecurity equation. Capable of great success, but also capable of massive failures. Education of end users is an on-going process, not just a 30-minute session once a year.
We also must be on-guard against abnormal activity of an authorized user. In many ways, Lapsus$ was successful because they weren't actively attempting to use intrusive exploits against targeted infrastructure. They were using legitimate credentials and organization approved toolsets to perform malicious activities. This is a weak point in many organizations security posture.
Rapid Development Cycles
IT organizations answer to their end users as a matter of course. This means that we have to navigate the fine line between responding quickly to security issues and enabling our end users to work uninterrupted. Threat actors on the other hand don't have red tape they need to cut. Threat actors don't have to schedule downtime.
We saw proof of just how this can affect an organization in January of 2021 when four zero day exploits were discovered in Microsoft Exchange server. Within days, threat actors were able to exploit thousands of servers across the world giving them full access to emails, passwords, and administrative access into the networks of affected organizations.
In just 3 months, over 250,000 servers were compromised. The most interesting thing about this attack was the speed at which hackers were able to react and begin exploiting the zero-days. The initial report to Microsoft of the vulnerabilities was on January 5th of 2021. The next day, the first server breach using these exploits was seen in the wild. By the end of the month, the exploits were being widely taken advantage of by multiple threat actors and ransomware attacks were on the rise.
There was no possible way for an organization to react fast enough to outpace the hackers without taking their email servers offline. Many did, but many decided to take the risk and paid a heavy price for it.
It took Microsoft until March 12th to institute a patch for these exploits. It took even longer for organizations to install that patch and clean up the affected servers. The primary victims of these attacks were identified by Microsoft as small and medium businesses and local government. Groups that often don't have the budget or the expertise on staff to deal with the attacks and mitigation in a timely manner.
Beyond Attacking the File System
A/V used to be easy! Notice some bad activity, scan the file system, find the bad file, delete the bad file, job done! Sure, sometimes the registry would get messed up, but we can fix that or just reinstall the OS. But over the past few years, something started to change. We stopped seeing the files in complex malware attacks, infections started to persist across OS re-installs, and we began to see more usage of malware hijacking native binaries that we couldn't delete without wrecking the affected systems.
For example, the Eternal Blue vulnerability was developed by the NSA and leaked by the Shadow Brokers hacking collective. It allows an attacker to send a couple of carefully crafted network packets to a windows server that creates the ability to run remote code on the targeted machine.
Once that little breach was successful, another NSA built tool called DoublePulsar would be ran on that system.
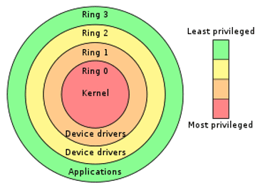
DoublePulsar is code that runs in Kernel mode on a server, meaning it has the absolute privilege to do anything it wants. It had 3 tools at its disposal:
- Ping: Allows it to do network reconnaissance.
- Kill: Allows it to disrupt any process that attempts to remove it from the system.
- Exec: Gives it the ability to download and install any package the threat actor wishes.
The impressive thing about this attack is not a single file exists on the targeted computer until it is too late and the breach is complete. The Double Pulsar backdoor simply exists as memory resident code. Traditional A/V simply doesn't have the capability to catch that.
Enter the era of Advanced A/V or Endpoint Detection and Response. Instead of looking at the files, look at the behavior of processes on the server. Look at the interactions and define what is "good" and "bad", then initiate a response to the bad ones.
This approach is a great leap forward but isn't able to detect malicious activity that isn't directly interacting with the OS. Recon and data exfiltration are still possible at the network layer without detection.
Tools that monitor the networks, the "space between" the servers are also necessary. Utilizing both toolsets creates a composite system for detecting and acting on cyber threats such as ransomware.
Dwell Time
Possibly the most important metric with regards to ransomware and malicious activity is dwell time, the length of time a threat actor has had in the network before being detected. During the dwell time, a threat actor is busy exfiltrating data, establishing a foothold in the environment, and escalating their privileges. The graph below shows the global median dwell time (in days), as reported in Mandiant's 2022 M-Trends report. In 2021, the median dwell time for external notifications decreased from 73 days to 28 days, while the median dwell time for internal notifications increased from 12 days to 18 days.
As corporations begin to implement technologies that aren't reliant on file system-based detection the likelihood of illicit activity being recognized quickly increases. Once we know about the attack, we can act on it and stop the activity, or utilize disaster recovery systems to reverse the damage done in the breach.
Early detection is critical to an organization's disaster response. Backup and DR mechanisms have a limited shelf life. Journals roll over, retentions are passed, and the longer an attacker has access to the systems, the more damage is being done.
Addressing the Issues
The rapid development and evolution of cyberattacks in todays world means we need to respond with care and choose our strategies wisely. We need to have a few key components in place to protect our organizations. Below is an outline of how we choose to layer protection technologies to create a complete protection plan:
Vulnerability and Patch Management
Most critical to pro-actively and continuously monitor for vulnerabilities and quickly patch them when found.
Acronis Cyber Protect provides OS level agents that scan both third party and Microsoft software to identify vulnerabilities, then patch those vulnerabilities in a rapid patching regimen.
End User Education and Authorized Use Management
Educating the end user has to be part of a protection plan. An entire industry has grown around automating testing a humans knowledge and their reaction to phishing and social engineering attacks. Knowbe4 is a great example of a "Security Awareness" services that can help to tighten down those security cracks in the user base.
DarkTrace provides a system based on "Patterns of Life" of each end user. Establishing a baseline for expected activity from each device/user pair, and alerting on any exception to that baseline.
OS Based EDR
OS based threat detection which has the ability to directly act upon the file system and process running on an endpoint will always be critical.
Carbon Black, DarkTrace, and Acronis all provide agent level EDR capabilities to provide process level anti-malware and exploit prevention.
Network Based Detection and Response
Supplementing OS based EDR with pattern based and AI driven network monitoring is somewhat new to the game but is proving to be invaluable when implemented.
DarkTrace provides monitoring for "the space between" devices, using artificial intelligence to identify and block attacks and exfiltration attempts.
Data Loss Prevention (DLP)
Exfiltrating data and threatening to leak it is the new failback by ransomware gangs in order to extort payment. You may be able to recover your data, but they still have it and can significantly harm your organization by releasing it.
Acronis provides data loss prevention at the agent level, allowing specific rules to be setup as to how and where data can be transferred both within and outside of the organization perimeter. This stops data exfiltration and alerts you to the attempts.
Backup
Archival retention of backup is still a key component of any solid protection plan. Acronis and Veeam, provide backup across the organization, including Office 365 and Google Workspaces. Backup should be maintained both on-premise for fast recovery and in cloud for catastrophic events that take down local systems entirely.
Immutability of these systems is critical, having a period of time in which no deletions can be made that is enforced outside of the backup application will prevent a threat actor from harming the last resort an organization has to recover from an event.
Disaster Recovery
When a threat actor is present in the environment, having a journaled disaster recovery solution that allows quick turn up of critical business components to a point before the breach is imperative. Backup is slow by nature, too slow to depend on in a crisis where you need the organization to be running at 100%.
Acronis and Zerto provide best in class disaster recovery solutions that provide low RPO's, fast RTO's, and seamless continuity of critical business components.
All organizations can struggle to maintain a solid security stance in the current threat landscape. Hopefully, these trends and resources can help prepare your IT team for current threats. If you need help getting started or are interesting in implementing one of these solutions, contact us at sales@n3t.com or Request More Info and we'd be happy to connect you with one of our Net3 Engineers.
